Tag: software vulnerability
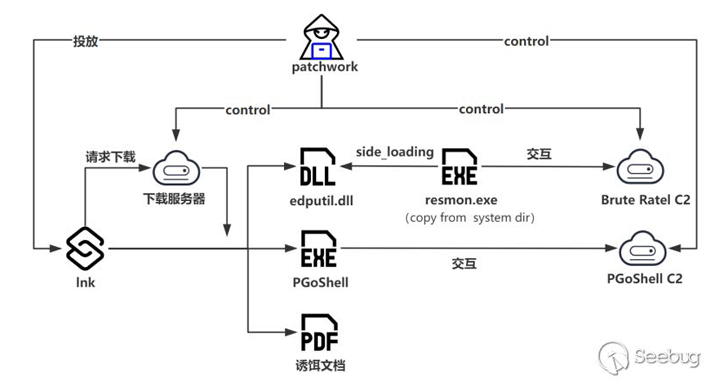
Jul 24, 2024NewsroomCyber Espionage / Threat Intelligence The threat actor known as Patchwork has been linked to a cyber attack targeting entities with ties to Bhutan to deliver the Brute Ratel C4 framework and an updated version of a backdoor called PGoShell. The development marks the first time the adversary has been observed using the…
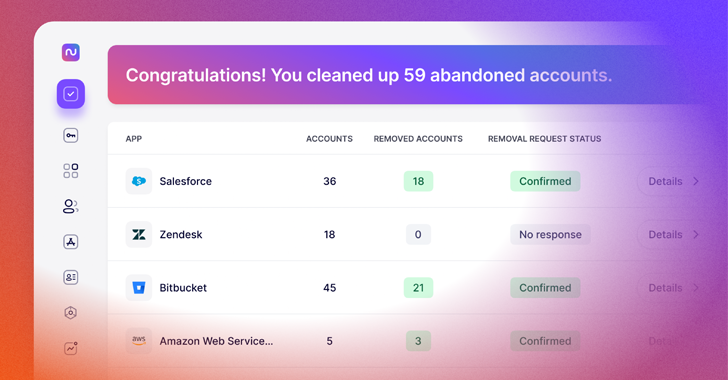
Read MoreJul 24, 2024The Hacker NewsSaaS Management / IT Governance There is one simple driver behind the modern explosion in SaaS adoption: productivity. We have reached an era where purpose-built tools exist for almost every aspect of modern business and it’s incredibly easy (and tempting) for your workforce to adopt these tools without going through the…
Read MoreJul 24, 2024NewsroomSoftware Update / IT Outage Cybersecurity firm CrowdStrike on Wednesday blamed an issue in its validation system for causing millions of Windows devices to crash as part of a widespread outage late last week. “On Friday, July 19, 2024 at 04:09 UTC, as part of regular operations, CrowdStrike released a content configuration update…
Read MoreJul 24, 2024NewsroomVulnerability / Software Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two security flaws to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerabilities are listed below – CVE-2012-4792 (CVSS score: 9.3) – Microsoft Internet Explorer Use-After-Free Vulnerability CVE-2024-39891 (CVSS score: 5.3) – Twilio Authy…
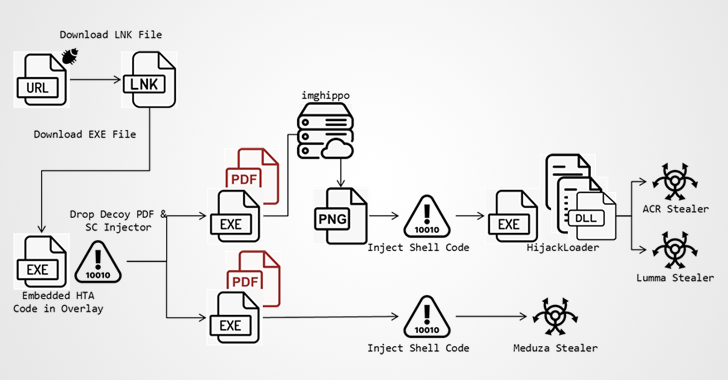
Read MoreJul 24, 2024NewsroomMalvertising / Threat Intelligence A now-patched security flaw in the Microsoft Defender SmartScreen has been exploited as part of a new campaign designed to deliver information stealers such as ACR Stealer, Lumma, and Meduza. Fortinet FortiGuard Labs said it detected the stealer campaign targeting Spain, Thailand, and the U.S. using booby-trapped files that…
Read MoreJul 23, 2024NewsroomCyber Espionage / Chinese Hackers Organizations in Taiwan and a U.S. non-governmental organization (NGO) based in China have been targeted by a Beijing-affiliated state-sponsored hacking group called Daggerfly using an upgraded set of malware tools. The campaign is a sign that the group “also engages in internal espionage,” Symantec’s Threat Hunter Team, part…
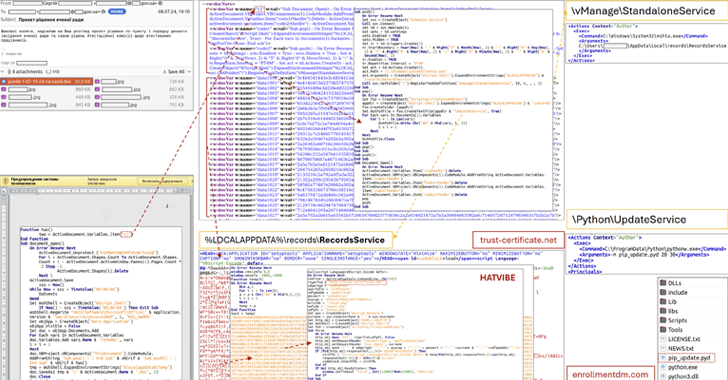
Read MoreJul 23, 2024NewsroomCyber Espionage / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has alerted of a spear-phishing campaign targeting a scientific research institution in the country with malware known as HATVIBE and CHERRYSPY. The agency attributed the attack to a threat actor it tracks under the name UAC-0063, which was previously observed targeting…
Read MoreJul 23, 2024NewsroomICS Malware / Critical Infrastructure Cybersecurity researchers have discovered what they say is the ninth Industrial Control Systems (ICS)-focused malware that has been used in a disruptive cyber attack targeting an energy company in the Ukrainian city of Lviv earlier this January. Industrial cybersecurity firm Dragos has dubbed the malware FrostyGoop, describing it…
Read MoreMeta has been given time till September 1, 2024, to respond to concerns raised by the European Commission over its “pay or consent” advertising model or risk-facing enforcement measures, including sanctions. The European Commission said the Consumer Protection Cooperation (CPC) Network has notified the social media giant of the model adopted on Facebook and Instagram…
Read MoreJul 23, 2024NewsroomThreat Detection / Website Security Threat actors have been observed using swap files in compromised websites to conceal a persistent credit card skimmer and harvest payment information. The sneaky technique, observed by Sucuri on a Magento e-commerce site’s checkout page, allowed the malware to survive multiple cleanup attempts, the company said. The skimmer…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm