Tag: software vulnerability
Jul 08, 2024NewsroomCyber Espionage / Cloud Security A previously undocumented advanced persistent threat (APT) group dubbed CloudSorcerer has been observed targeting Russian government entities by leveraging cloud services for command-and-control (C2) and data exfiltration. Cybersecurity firm Kaspersky, which discovered the activity in May 2024, the tradecraft adopted by the threat actor bears similarities with that…
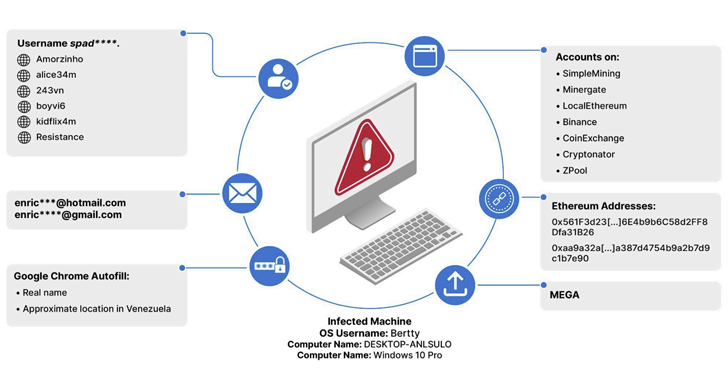
Read MoreJul 08, 2024NewsroomDark Web / Cyber Crime An analysis of information-stealing malware logs published on the dark web has led to the discovery of thousands of consumers of child sexual abuse material (CSAM), indicating how such information could be used to combat serious crimes. “Approximately 3,300 unique users were found with accounts on known CSAM…
Read MoreJul 08, 2024NewsroomRansomware / Encryption An emerging ransomware-as-a-service (RaaS) operation called Eldorado comes with locker variants to encrypt files on Windows and Linux systems. Eldorado first appeared on March 16, 2024, when an advertisement for the affiliate program was posted on the ransomware forum RAMP, Singapore-headquartered Group-IB said. The cybersecurity firm, which infiltrated the ransomware…
Read MoreJul 08, 2024The Hacker NewsCybersecurity / Enterprise Security Events like the recent massive CDK ransomware attack – which shuttered car dealerships across the U.S. in late June 2024 – barely raise public eyebrows anymore. Yet businesses, and the people that lead them, are justifiably jittery. Every CISO knows that cybersecurity is an increasingly hot topic…
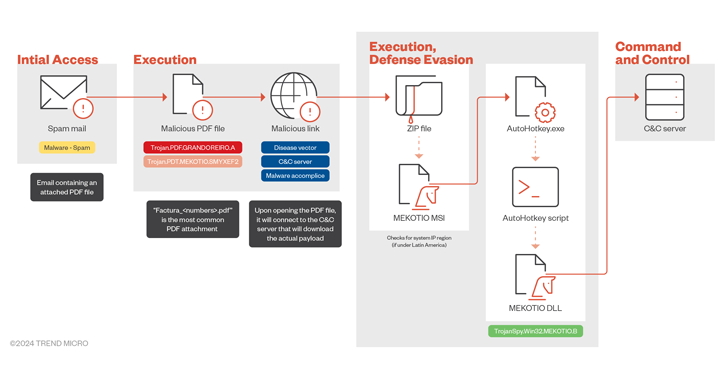
Read MoreJul 08, 2024NewsroomMalware / Cyber Threat Financial institutions in Latin America are being threatened by a banking trojan called Mekotio (aka Melcoz). That’s according to findings from Trend Micro, which said it recently observed a surge in cyber attacks distributing the Windows malware. Mekotio, known to be actively put to use since 2015, is known…
Read MoreJul 08, 2024NewsroomVulnerability / Software Security Four unpatched security flaws, including three critical ones, have been disclosed in the Gogs open-source, self-hosted Git service that could enable an authenticated attacker to breach susceptible instances, steal or wipe source code, and even plant backdoors. The vulnerabilities, according to SonarSource researchers Thomas Chauchefoin and Paul Gerste, are…
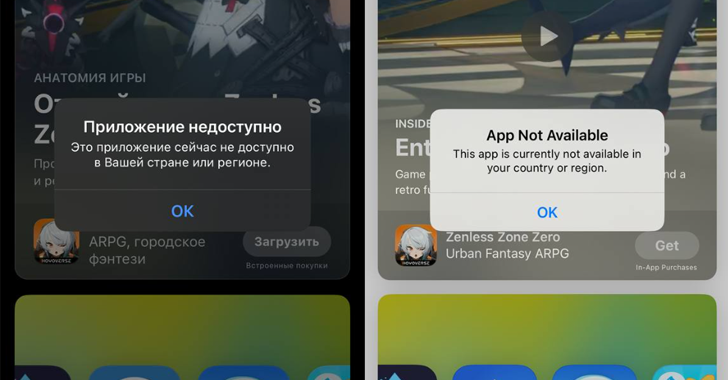
Read MoreJul 08, 2024NewsroomPrivacy / Internet Censorship Apple removed a number of virtual private network (VPN) apps in Russia from its App Store on July 4, 2024, following a request by Russia’s state communications watchdog Roskomnadzor, Russian news media reported. This includes the mobile apps of 25 VPN service providers, including ProtonVPN, Red Shield VPN, NordVPN…
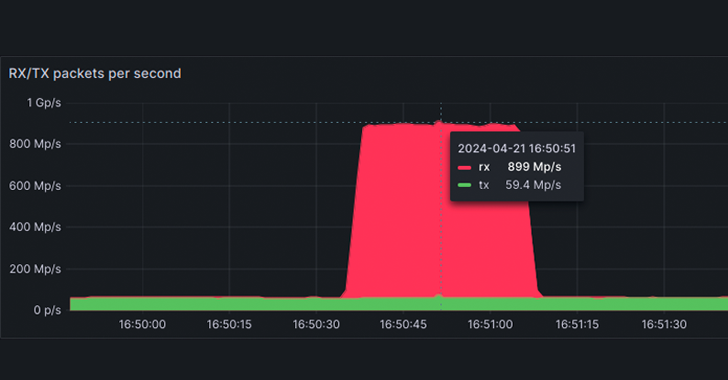
Read MoreJul 05, 2024NewsroomNetwork Security / DDoS Attack French cloud computing firm OVHcloud said it mitigated a record-breaking distributed denial-of-service (DDoS) attack in April 2024 that reached a packet rate of 840 million packets per second (Mpps). This is just above the previous record of 809 million Mpps reported by Akamai as targeting a large European…
Read MoreJul 05, 2024The Hacker NewsCybersecurity / Identity Protection Identity theft isn’t just about stolen credit cards anymore. Today, cybercriminals are using advanced tactics to infiltrate organizations and cause major damage with compromised credentials. The stakes are high: ransomware attacks, lateral movement, and devastating data breaches. Don’t be caught off guard. Join us for a groundbreaking…
Read MoreJul 05, 2024The Hacker NewsCloud Security / Attack Surface The attack surface isn’t what it once was and it’s becoming a nightmare to protect. A constantly expanding and evolving attack surface means risk to the business has skyrocketed and current security measures are struggling to keep it protected. If you’ve clicked on this article, there’s…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm