Cyber attacks involving the DarkGate malware-as-a-service (MaaS) operation have shifted away from AutoIt scripts to an AutoHotkey mechanism to deliver the last stages, underscoring continued efforts on the part of the threat actors to continuously stay ahead of the detection curve.
The updates have been observed in version 6 of DarkGate released in March 2024 by its developer RastaFarEye, who has been selling the program on a subscription basis to as many as 30 customers. The malware has been active since at least 2018.
A fully-featured remote access trojan (RAT), DarkGate is equipped with command-and-control (C2) and rootkit capabilities, and incorporates various modules for credential theft, keylogging, screen capturing, and remote desktop.
“DarkGate campaigns tend to adapt really fast, modifying different components to try to stay off security solutions,” Trellix security researcher Ernesto Fernández Provecho said in a Monday analysis. “This is the first time we find DarkGate using AutoHotKey, a not so common scripting interpreter, to launch DarkGate.”
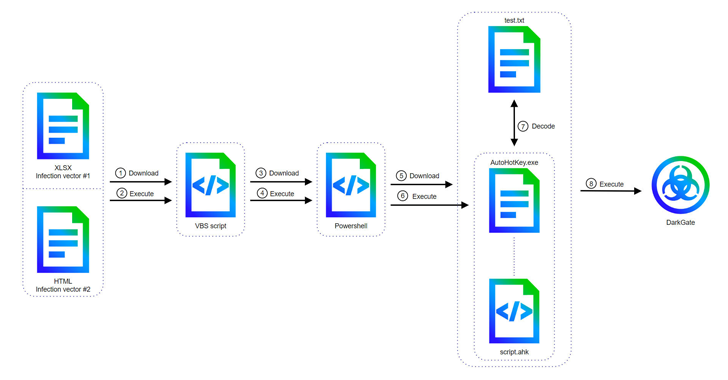
It’s worth noting that DarkGate’s switch to AutoHotKey was first documented by McAfee Labs in late April 2024, with attack chains leveraging security flaws such as CVE-2023-36025 and CVE-2024-21412 to bypass Microsoft Defender SmartScreen protections using a Microsoft Excel or an HTML attachment in phishing emails.
Alternate methods have been found to leverage Excel files with embedded macros as a conduit to execute a Visual Basic Script file that’s responsible for invoking PowerShell commands to ultimately launch an AutoHotKey script, which, in turn, retrieves and decodes the DarkGate payload from a text file.
The latest version of DarkGate packs in substantial upgrades to its configuration, evasion techniques, and the list of supported commands, which now includes audio recording, mouse control, and keyboard management features.
“Version 6 not only includes new commands, but also lacks some of them from previous versions, like the privilege escalation, the cryptomining, or the hVNC (Hidden Virtual Network Computing) ones,” Fernández Provecho said, adding it may be an effort to cut out features that could enable detection.
“Moreover, since DarkGate is sold to a small group of people, it is also possible that the customers were not interested in those features, forcing RastaFarEye to remove them.”
The disclosure comes as cyber criminals have been found abusing Docusign by selling legitimate-looking customizable phishing templates on underground forums, turning the service into a fertile ground for phishers looking to steal credentials for phishing and business email compromise (BEC) scams.
“These fraudulent emails, meticulously designed to mimic legitimate document signing requests, lure unsuspecting recipients into clicking malicious links or divulging sensitive information,” Abnormal Security said.