Gitloker attacks abuse GitHub notifications to push malicious oAuth apps
by nlqip
Threat actors impersonate GitHub’s security and recruitment teams in phishing attacks to hijack repositories using malicious OAuth apps in an ongoing extortion campaign wiping compromised repos.
Since at least February, dozens of developers targeted in this campaign have received similar fake job offers or security alert emails from “notifications@github.com” after being tagged in spam comments added to random repo issues or pull requests using compromised GitHub accounts.
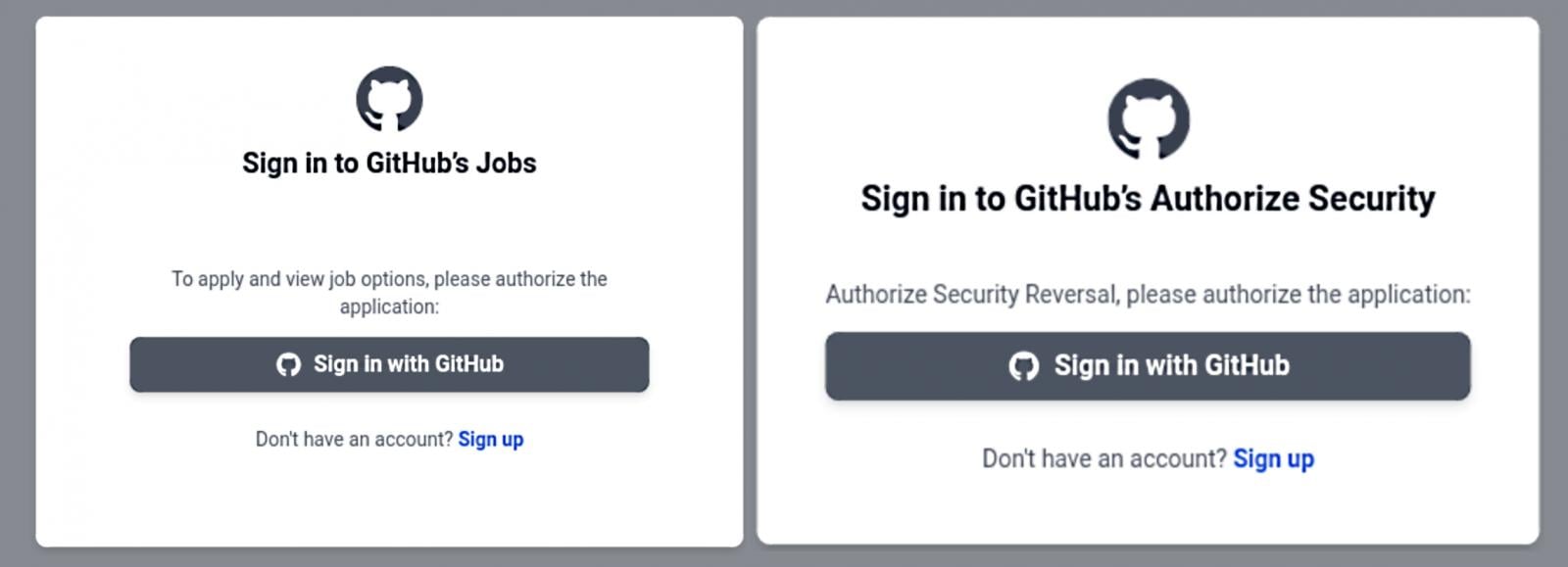
The phishing emails redirect potential victims to githubcareers[.]online or githubtalentcommunity[.]online, as first spotted by CronUp security researcher Germán Fernández.
On the landing pages, users are asked to sign into their GitHub accounts to authorize a new OAuth app that requests access to private repositories, personal user data, and the ability to delete any adminable repository, among other things.
Many GitHub users who have fallen victim to these attacks also report having their accounts disabled and losing access to all repos—likely after other victims reported them for being abused to push comment spam.
As BleepingComputer reported on Thursday, after gaining access to the victims’ repositories, the attackers wipe the contents, rename the repository, and add a README.me file instructing the victims to reach out on Telegram to recover the data.
They also claim to have stolen the victims’ data before destroying it and created a backup that could help restore the wiped repositories.
BleepingComputer has yet to receive a reply from a GitHub spokesperson after reaching out last week for more details regarding the Gitloker extortion campaign.
However, GitHub staff has been replying to community discussions about these attacks since February, saying the campaign targets GitHub’s mention and notification functionality and asking those targeted to report this malicious activity using the coding platform’s abuse reporting tools.
“We understand the inconvenience caused by these notifications. Our teams are currently working on addressing these unsolicited phishing notifications,” one GitHub community manager said.
“We want to remind our users to continue to use our abuse reporting tools to raise any abusive or suspicious activity. This is a phishing campaign and is not the result of a compromise of GitHub or its systems.”
GitHub staff also advised users to take the following measures to ensure their accounts aren’t hijacked in these attacks:
In September 2020, GitHub warned of another phishing campaign using emails pushing fake CircleCI notifications to steal GitHub credentials and two-factor authentication (2FA) codes by relaying them through reverse proxies.
Source link
lol
Threat actors impersonate GitHub’s security and recruitment teams in phishing attacks to hijack repositories using malicious OAuth apps in an ongoing extortion campaign wiping compromised repos. Since at least February, dozens of developers targeted in this campaign have received similar fake job offers or security alert emails from “notifications@github.com” after being tagged in spam comments…
Recent Posts
- French Authorities Launch Operation to Remove PlugX Malware from Infected Systems
- Malicious PyPI Package Targets macOS to Steal Google Cloud Credentials
- Secure Boot no more? Leaked key, faulty practices put 900 PC/server models in jeopardy
- Crooks Bypassed Google’s Email Verification to Create Workspace Accounts, Access 3rd-Party Services – Krebs on Security
- Friday Squid Blogging: Sunscreen from Squid Pigments
