West Burton Energy Leverages Tenable OT Security To Improve Security, Safety and Efficiency
by nlqip
Tenable®, the Exposure Management company, today announced West Burton Energy is using Tenable OT Security to deliver operational technology (OT) asset visibility, OT vulnerability management, and threat detection – use cases that have proven challenging for so many companies in the power industry. This has enabled West Burton Energy to reduce threat-detection alerts by 98% and improve…
Read MoreOn the morning of August 30, 2023, a fire broke out at a data center operated by Belgian telecom giant Proximus. Soon, emergency numbers 112, 101, and 100, which are used to call the ambulance, the firefighters, and the police, became unreachable. The situation lasted for almost half an hour before these essential services were…
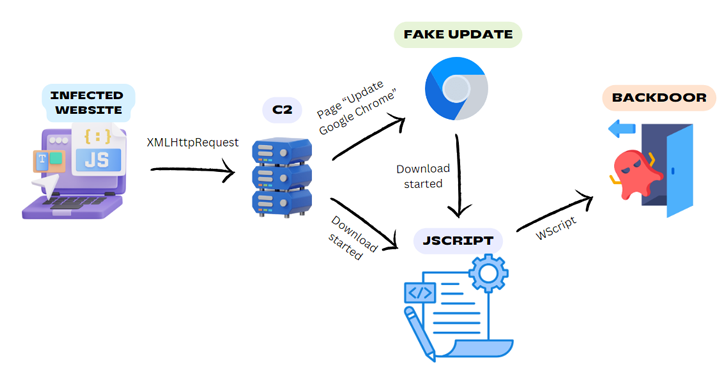
Read MoreJun 17, 2024NewsroomWeb Security / Malware Legitimate-but-compromised websites are being used as a conduit to deliver a Windows backdoor dubbed BadSpace under the guise of fake browser updates. “The threat actor employs a multi-stage attack chain involving an infected website, a command-and-control (C2) server, in some cases a fake browser update, and a JScript downloader…
Read MorePerhaps the best way to understand the approach is with an analogy about childhood learning. When we tell toddlers about numbers, they have no idea about how they drive complex human activities (statistical analysis, for instance). Instead, numbers are words learned perhaps by memorizing a song that uses them ( “One, Two, Buckle My Shoe”).…
Read MoreJun 17, 2024NewsroomBotnet / Cryptocurrency Threat actors have been observed deploying a malware called NiceRAT to co-opt infected devices into a botnet. The attacks, which target South Korean users, are designed to propagate the malware under the guise of cracked software, such as Microsoft Windows, or tools that purport to offer license verification for Microsoft…
Read MoreAs if CSOs didn’t have enough to worry about, how about upwards of four million more ways that cybercriminals could affect businesses — and society in general — through attacks on spacecraft and the infrastructure that develops, launches, and supports them? That’s what a new study from the Ethics + Emerging Sciences Group at California…
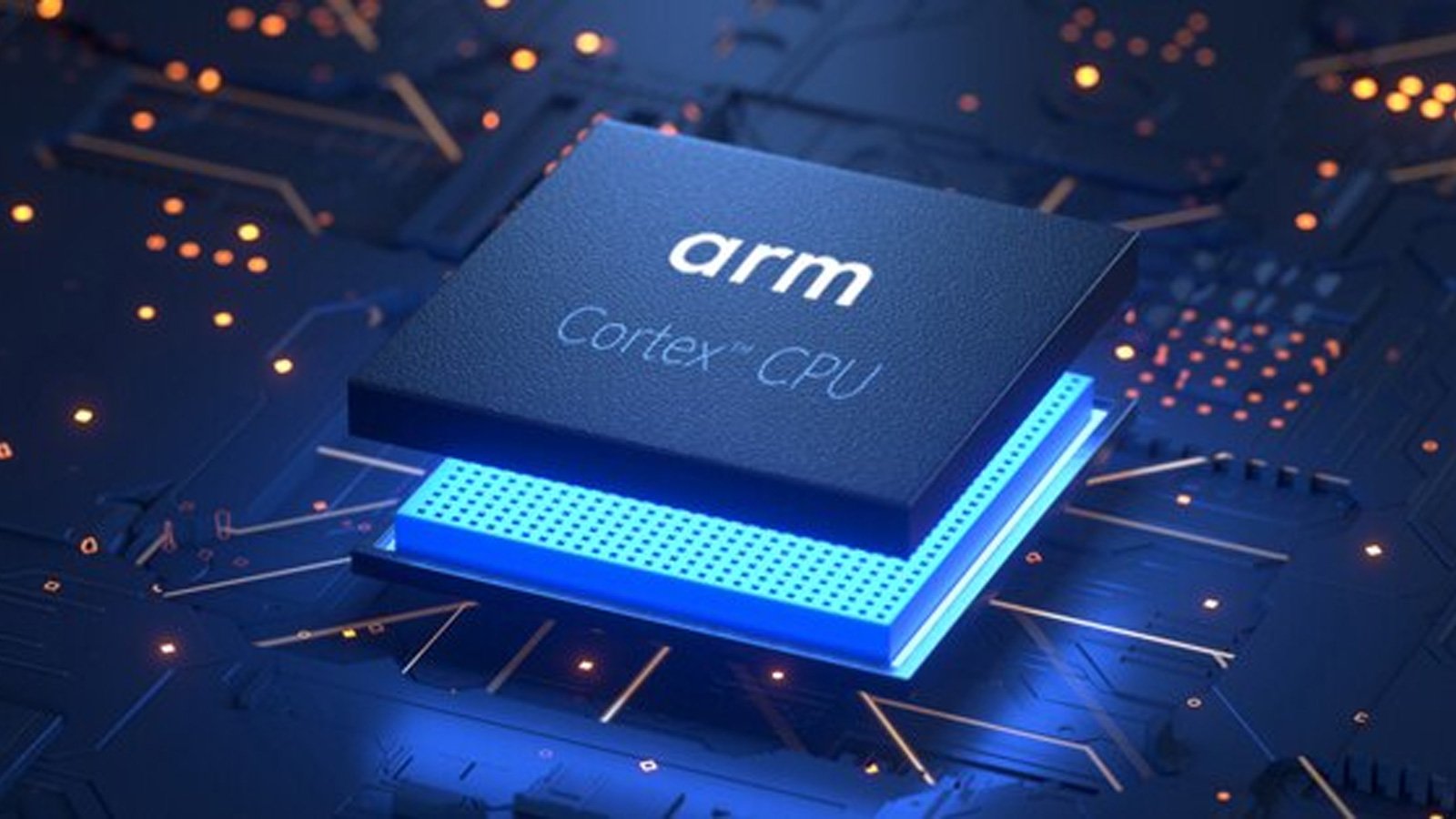
Read MoreA new speculative execution attack named “TIKTAG” targets ARM’s Memory Tagging Extension (MTE) to leak data with over a 95% chance of success, allowing hackers to bypass the security feature. The paper, co-signed by a team of Korean researchers from Samsung, Seoul National University, and the Georgia Institute of Technology, demonstrates the attack against Google Chrome…
Read MoreJun 16, 2024NewsroomCybercrime / SIM Swapping Law enforcement authorities have allegedly arrested a key member of the notorious cybercrime group called Scattered Spider. The individual, a 22-year-old man from the United Kingdom, was arrested this week in the Spanish city of Palma de Mallorca as he attempted to board a flight to Italy. The move…
Read MoreA 22-year-old man from the United Kingdom arrested this week in Spain is allegedly the ringleader of Scattered Spider, a cybercrime group suspected of hacking into Twilio, LastPass, DoorDash, Mailchimp, and nearly 130 other organizations over the past two years. The Spanish daily Murcia Today reports the suspect was wanted by the FBI and arrested…
Read MoreMicrosoft has announced new cybersecurity enhancements for Outlook personal email accounts as part of its ‘Secure Future Initiative,’ including the deprecation of basic authentication (username + password) by September 16, 2024. The software giant also announced the end of support for ‘Mail’ and ‘Calendar’ apps on Windows, the deprecation of Outlook Light, and removing users’ ability…
Read MoreRecent Posts
- Safeguarding Healthcare Organizations from IoMT Risks
- Broadcom’s VMware Issues ‘Top of Mind’ For Partners, Nutanix Channel Chief Says
- Microsoft just killed the Windows 10 Beta Channel again
- Fraud network uses 4,700 fake shopping sites to steal credit cards
- CISA warns of more Palo Alto Networks bugs exploited in attacks