Tag: how to hack
May 23, 2024NewsroomEndpoint Security / Data Privacy Microsoft on Wednesday outlined its plans to deprecate Visual Basic Script (VBScript) in the second half of 2024 in favor of more advanced alternatives such as JavaScript and PowerShell. “Technology has advanced over the years, giving rise to more powerful and versatile scripting languages such as JavaScript and…
Read MoreCybersecurity researchers have disclosed details of a previously undocumented threat group called Unfading Sea Haze that’s believed to have been active since 2018. The intrusion singled out high-level organizations in South China Sea countries, particularly military and government targets, Bitdefender said in a report shared with The Hacker News. “The investigation revealed a troubling trend…
Read MoreMay 22, 2024NewsroomICS Security / Vulnerability Rockwell Automation is urging its customers to disconnect all industrial control systems (ICSs) not meant to be connected to the public-facing internet to mitigate unauthorized or malicious cyber activity. The company said it’s issuing the advisory due to “heightened geopolitical tensions and adversarial cyber activity globally.” To that end,…
Read MoreSince the first edition of The Ultimate SaaS Security Posture Management (SSPM) Checklist was released three years ago, the corporate SaaS sprawl has been growing at a double-digit pace. In large enterprises, the number of SaaS applications in use today is in the hundreds, spread across departmental stacks, complicating the job of security teams to…
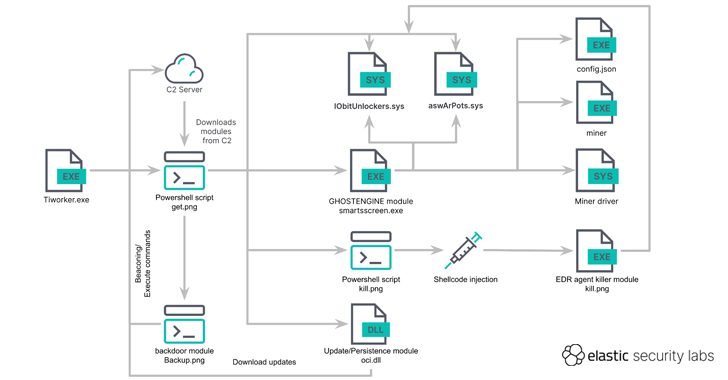
Read MoreCybersecurity researchers have discovered a new cryptojacking campaign that employs vulnerable drivers to disable known security solutions (EDRs) and thwart detection in what’s called a Bring Your Own Vulnerable Driver (BYOVD) attack. Elastic Security Labs is tracking the campaign under the name REF4578 and the primary payload as GHOSTENGINE. Previous research from Chinese cybersecurity firm…
Read MoreMay 22, 2024NewsroomVulnerability / Data Breach An unknown threat actor is exploiting known security flaws in Microsoft Exchange Server to deploy a keylogger malware in attacks targeting entities in Africa and the Middle East. Russian cybersecurity firm Positive Technologies said it identified over 30 victims spanning government agencies, banks, IT companies, and educational institutions. The…
Read MoreMay 22, 2024NewsroomEncryption / Quantum Computing Popular enterprise services provider Zoom has announced the rollout of post-quantum end-to-end encryption (E2EE) for Zoom Meetings, with support for Zoom Phone and Zoom Rooms coming in the future. “As adversarial threats become more sophisticated, so does the need to safeguard user data,” the company said in a statement.…
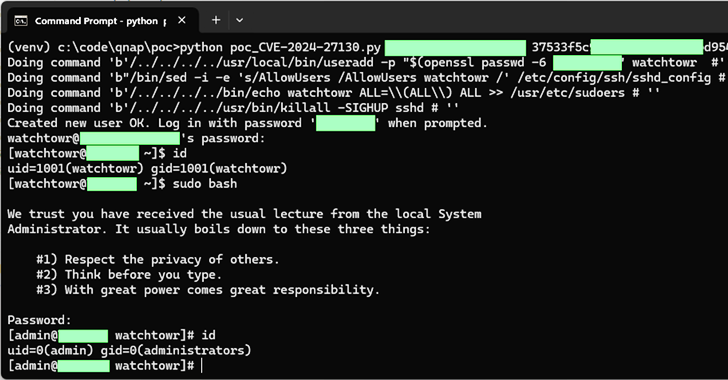
Read MoreMay 22, 2024NewsroomData Security / Vulnerability Taiwanese company QNAP has rolled out fixes for a set of medium-severity flaws impacting QTS and QuTS hero, some of which could be exploited to achieve code execution on its network-attached storage (NAS) appliances. The issues, which impact QTS 5.1.x and QuTS hero h5.1.x, are listed below – CVE-2024-21902…
Read MoreMay 22, 2024NewsroomEnterprise Security / Vulnerability Users of Veeam Backup Enterprise Manager are being urged to update to the latest version following the discovery of a critical security flaw that could permit an adversary to bypass authentication protections. Tracked as CVE-2024-29849 (CVSS score: 9.8), the vulnerability could allow an unauthenticated attacker to log in to…
Read MoreMay 21, 2024NewsroomVulnerability / Software Development GitHub has rolled out fixes to address a maximum severity flaw in the GitHub Enterprise Server (GHES) that could allow an attacker to bypass authentication protections. Tracked as CVE-2024-4985 (CVSS score: 10.0), the issue could permit unauthorized access to an instance without requiring prior authentication. “On instances that use…
Read MoreRecent Posts
- Bob Sullivan Discovers a Scam That Strikes Twice
- A Vulnerability in Apache Struts2 Could Allow for Remote Code Execution
- CISA Adds One Known Exploited Vulnerability to Catalog | CISA
- Xerox To Buy Lexmark For $1.5B In Blockbuster Print Deal
- Vulnerability Summary for the Week of December 16, 2024 | CISA