Tag: network security
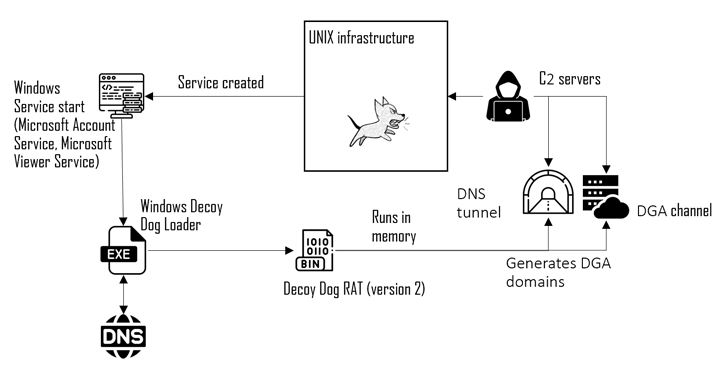
Jun 04, 2024NewsroomCyber Attack / Malware Russian organizations are at the receiving end of cyber attacks that have been found to deliver a Windows version of a malware called Decoy Dog. Cybersecurity company Positive Technologies is tracking the activity cluster under the name Operation Lahat, attributing it to an advanced persistent threat (APT) group called…
Read MoreJun 04, 2024NewsroomServer Security / Vulnerability Progress Software has rolled out updates to address a critical security flaw impacting the Telerik Report Server that could be potentially exploited by a remote attacker to bypass authentication and create rogue administrator users. The issue, tracked as CVE-2024-4358, carries a CVSS score of 9.8 out of a maximum…
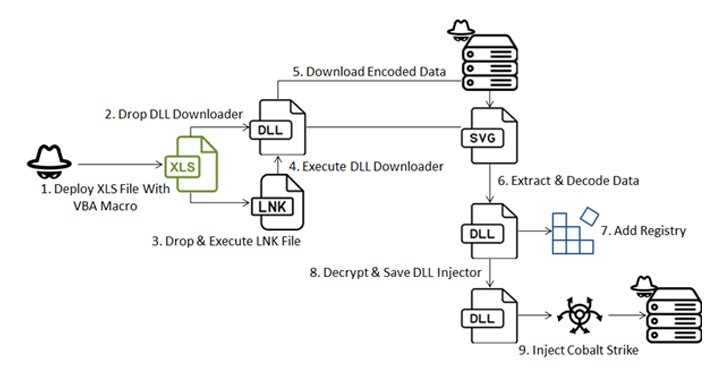
Read MoreJun 04, 2024NewsroomCyber Attack / Malware A new sophisticated cyber attack has been observed targeting endpoints geolocated to Ukraine with an aim to deploy Cobalt Strike and seize control of the compromised hosts. The attack chain, per Fortinet FortiGuard Labs, involves a Microsoft Excel file that carries an embedded VBA macro to initiate the infection,…
Read MoreJun 04, 2024The Hacker NewsBrowser Security / Enterprise Security The landscape of browser security has undergone significant changes over the past decade. While Browser Isolation was once considered the gold standard for protecting against browser exploits and malware downloads, it has become increasingly inadequate and insecure in today’s SaaS-centric world. The limitations of Browser Isolation,…
Read MoreJun 04, 2024NewsroomCloud Security / Data Protection Cloud computing and analytics company Snowflake said a “limited number” of its customers have been singled out as part of a targeted campaign. “We have not identified evidence suggesting this activity was caused by a vulnerability, misconfiguration, or breach of Snowflake’s platform,” the company said in a joint…
Read MorePenetration testing is a cornerstone of any mature security program and is a mature and well understood practice supported by robust methodologies, tools, and frameworks. The tactical goals of these engagements typically revolve around identification and exploitation of vulnerabilities in technology, processes, and people to gain initial, elevated, and administrative access to the target environment.…
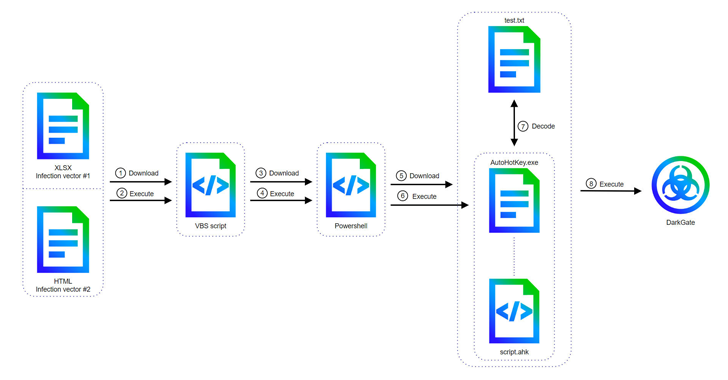
Read MoreJun 04, 2024NewsroomVulnerability / Threat Intelligence Cyber attacks involving the DarkGate malware-as-a-service (MaaS) operation have shifted away from AutoIt scripts to an AutoHotkey mechanism to deliver the last stages, underscoring continued efforts on the part of the threat actors to continuously stay ahead of the detection curve. The updates have been observed in version 6…
Read MoreJun 04, 2024NewsroomNetwork Security / Cryptocurrency The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a security flaw impacting the Oracle WebLogic Server to the Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. Tracked as CVE-2017-3506 (CVSS score: 7.4), the issue concerns an operating system (OS) command injection vulnerability that could…
Read More‘CISOs that have been struggling with security and compliance tell us all the time that this is exactly what they need,’ says Aqueduct Technologies CTO Shane O’Brien. ‘This is a compliance game changer for customers.’ Aqueduct Technologies Chief Technology Officer Shane O’Brien is no longer surprised by the look of amazement he gets from CISOs…
Read MoreJun 03, 2024NewsroomMalware / Cybercrime Law enforcement authorities behind Operation Endgame are seeking information related to an individual who goes by the name Odd and is allegedly the mastermind behind the Emotet malware. Odd is also said to go by the nicknames Aron, C700, Cbd748, Ivanov Odd, Mors, Morse, Veron over the past few years,…
Read MoreRecent Posts
- CISA Releases the Cybersecurity Performance Goals Adoption Report | CISA
- Multiple vulnerabilities in SonicWall SonicOS could allow a remote attacker to bypass authentication.
- Dell Sales Leader, Former Channel Chief John Byrne Steps Down
- The Dangers of DNS Hijacking
- CES 2025: 15 PC Chips Announced By Intel, Nvidia, AMD And Qualcomm